Meltdown, performance before and after
-
If anyone is in the vineyard, this is what's happening.
As they have said outside the forum, it would be interesting to evaluate the impact of the patch for Windows on our micros. My home PC is a Xeon E5472 that, although according to Intel it is not affected, I have decided to check if it was true.
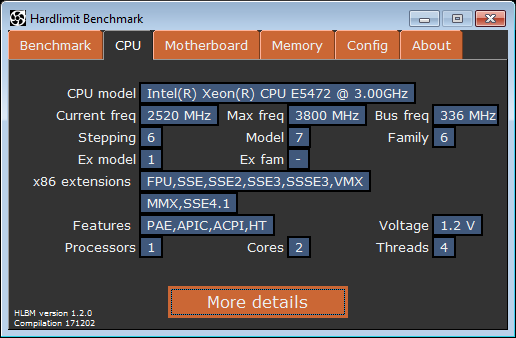
I have used SuperPI and another benchmark that I think I have never talked about: the Hardlimit benchmark. In theory SuperPi should not show any difference but I am not very sure about HLBM. Perhaps test #3 (de/compression in zip) might show some symptoms.
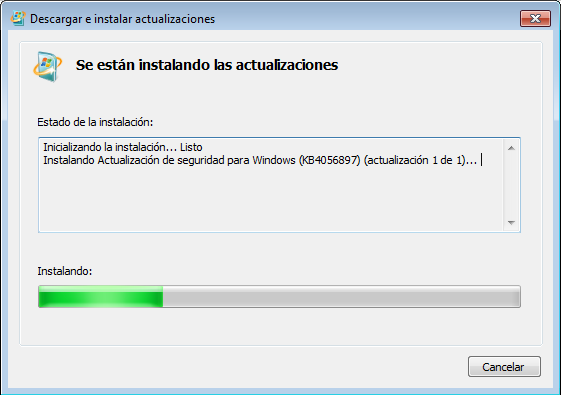
I use Windows 7 64-bit, so the patch published yesterday is the KB4056897. For Windows 10 it is the KB4056892.
HLBM
Monohilo Multihilo Validación FPU antes 15469 44966 Link FPU después 15551 44819 Link SSE3 antes 16766 49425 Link SSE3 después 16700 49836 Link As you can see, the variations are purely statistical so there is nothing interesting to show.
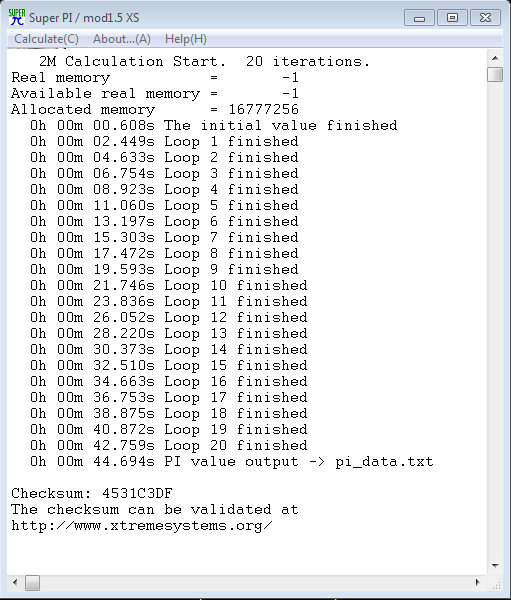
Super Pi
Before
After
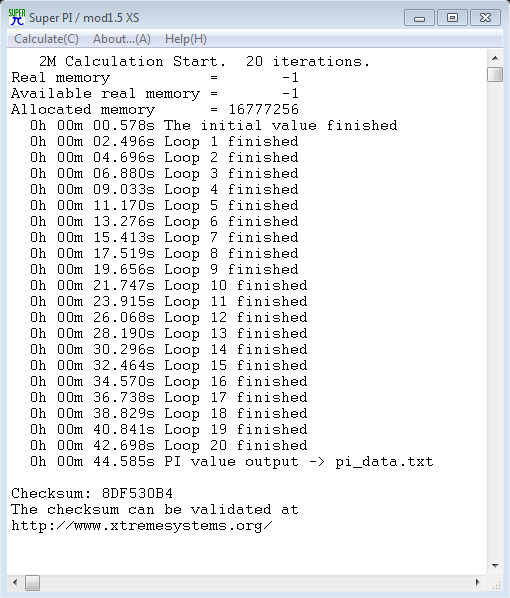
Another completely irrelevant result. I don't have any modern PC at hand, so for my part, this is what I can offer.
If you come up with any other benchmark that can show palpable differences, don't hesitate to put it down.
-
First of all, I was surprised that the darn patch didn't come out through Windows update.
Second, at least during the test (by default in mode II(AVX), the result hardly varies between before and after.
I don't know where they got the up to 30% performance decrease from, maybe they have the same level of math skills as I do. -
On an i7-5500U it can be seen that there is no difference.
Although there have been reports of performance decreases in databases and AWS users are complaining that they have noticed everything being slower, for the average person who doesn't use virtualization, nothing has happened here. At least in the use of CPU+memory (without taking into account storage devices or other hardware).
-
Well, I passed my results. Tested on a i7 4790K 4.0GHz / 16Gb / GTX970 / Win10 64bits system. Without any optimization. Running the benchmarks as is (without deleting residents, background processes, etc.).
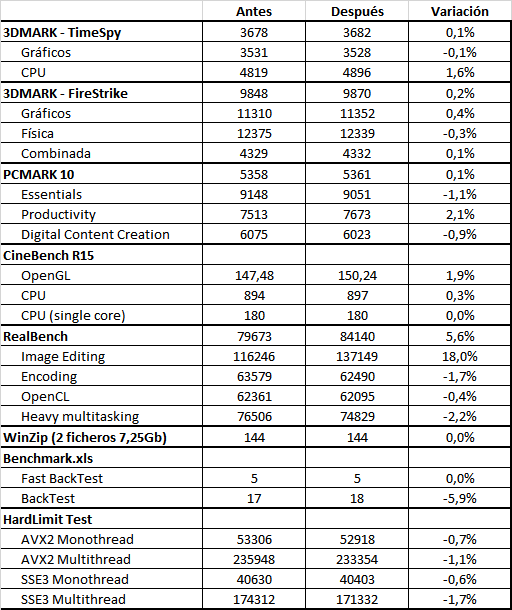
As you can see, no significant variation. In the case of RealBench and our test, I passed it three times and calculated the averages, because they give significant variations in each execution. Noticeable in the case of the HL test and quite large in the case of RealBench.
I suppose this set of tests gives a fairly broad view of different processor uses (although something closer to in-game tests would be missing) and, as you can see, the installation of the patch does not seem to have any significant impact on this configuration.
-
Microsoft states that the patch may affect performance. It seems that this first patch covers Meltdown and one of the Spectre variants and does not affect performance, but resolving the second variant involves stopping speculative processing in certain circumstances and necessarily has to affect it.
Here the entry in the Microsoft blog.
-
Extract from the link posted by @lforos:
· With Windows 10 on new processors (2016 PCs with Skylake, Kabylake or newer processors), the benchmarks show single-digit slowdowns but we don't expect most users to notice the change because those percentages translate to milliseconds.
· With Windows 10 on older processors (2015 PCs or earlier like Haswell), some benchmarks show a more significant slowdown and we expect some users to notice a performance decrease.
· With Windows 8 and Windows 7 on older processors (2015 PCs or earlier like Haswell) we expect most users to notice a performance decrease.
· With Windows Server on any processors, especially in I/O-intensive applications, there is a significant performance impact when mitigations are enabled to isolate untrusted code in a Windows Server instance. So you should carefully evaluate the risk of untrusted code in each Windows Server instance and balance security and performance.
It seems that Windows Server behaves in a similar way to Linux. The advice to properly evaluate the performance/security balance is noteworthy; the penalty must be significant there. And since they don't specify the scope of the tests and considering that Windows 7/8/10 are aimed at the general public (nothing like intensive use of virtual machines, databases, etc.), the issue doesn't look too good.
It's also curious that on micros produced since 2016, the impact is less and in that same explanation they say why:
To put it in context, on more modern processors like Skylake and later, Intel has refined the instructions to disable branch speculation to be more specific in indirect branches, reducing the performance penalty of the Spectre patch.
I read somewhere that last summer the head of practically all architectures since Conroe (the latest ones more than 10 years old) had left Intel without giving too many explanations. That is, this should have been known for quite some time.
And about Windows prior to 10, their explanation is that these systems tend to perform more operations on the kernel.
Anyway, it seems that the mess is not over.
-
@cobito said in Meltdown, performance before and after:
Extract from the link that @lforos has published:
· With Windows 10 on new processors (PCs from 2016 with Skylake, Kabylake or more recent processors), the test benches show single-digit slowdowns but we don't expect most users to notice the change because those percentages are reflected in milliseconds.
· With Windows 10 on older processors (PCs from 2015 or earlier such as Haswell), some test benches show a more significant slowdown and we expect some users to notice a decrease in performance.
· With Windows 8 and Windows 7 on older processors (PCs from 2015 or earlier such as Haswell) we expect most users to notice a decrease in performance.
· With Windows Server on any processors, especially in applications with intensive I/O use, a significant impact on performance is shown when mitigations are enabled to isolate untrusted code in a Windows Server instance. That's why you should be careful when evaluating the risk of untrusted code in each Windows Server instance and balance security and performance.
It seems that Windows Server behaves in a similar way to Linux. The advice to properly evaluate the performance/security balance is noteworthy; the penalty should be significant there. And since they don't specify the scope of the tests and considering that Windows 7/8/10 are intended for the general public (nothing about intensive use of virtual machines, databases, etc.), the issue doesn't look too good.
It's also curious that in micros produced since 2016, the impact is less and in that same explanation they say why:
To put it in context, in more modern processors such as Skylake and later, Intel has refined the instructions to disable branch speculation to be more specific in indirect branches reducing the performance penalty of the patch for Spectre.
I read that last summer the person in charge of practically all architectures since Conroe (the latest more than 10 years ago) left Intel without giving too many explanations. That is, this should have been known for quite some time.
And about Windows prior to 10, the explanation according to them is that these systems tend to perform more operations on the kernel.
Anyway, it seems that the problem is not over.
To me, this smells 100% like it's an "indirect" way of forcing everyone to use Windows 10, killing the performance of W7 and W8.
Personally, I only had W10 on my main computer, the other 2 that I have that are more occasional have win7 mainly because otherwise every time I turned them on they would spend more time updating than running.